Overview
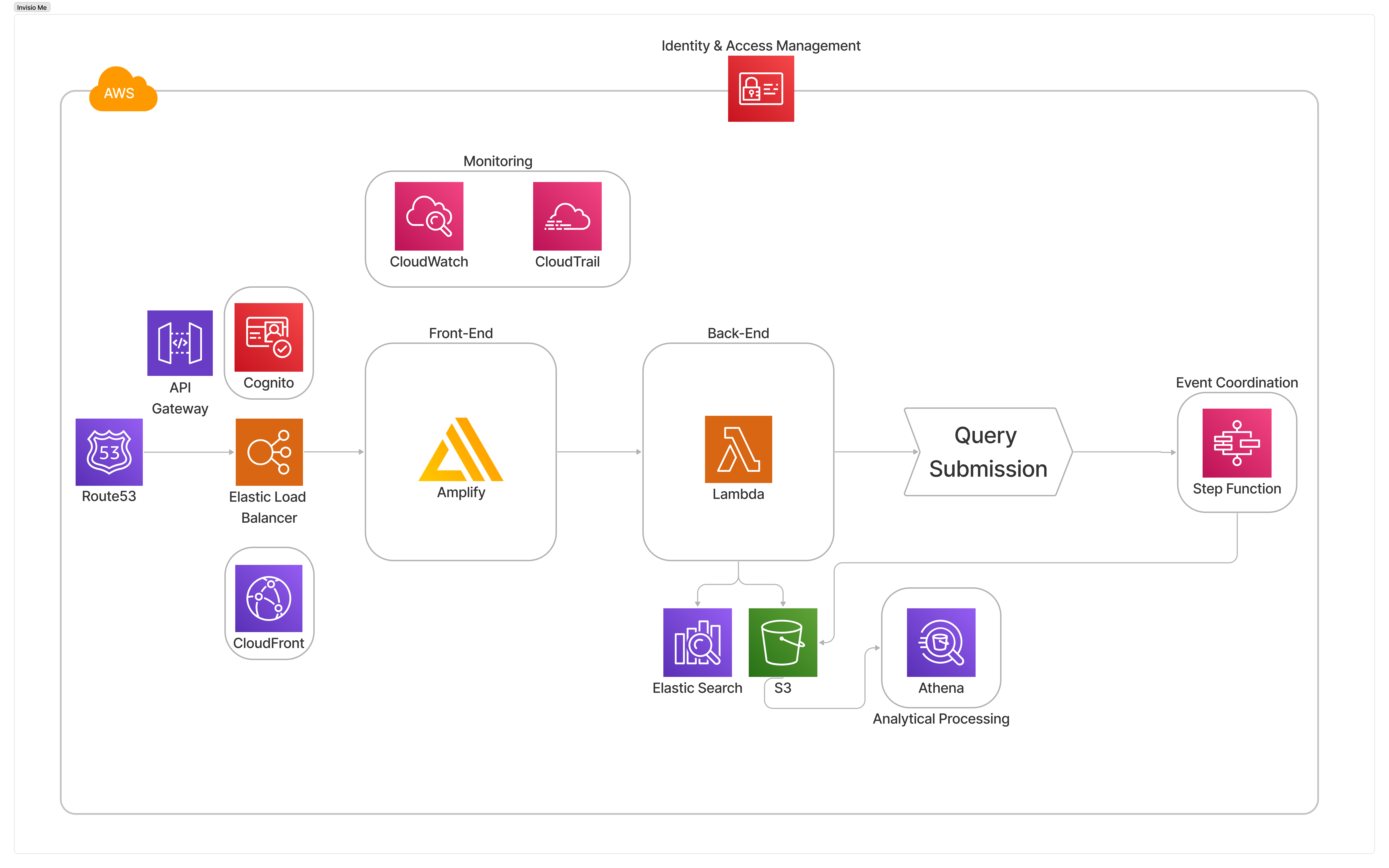
Invisio Me is my cloud-native privacy automation tool inspired by services like Incogni. Built on AWS, it enables users to automate data removal requests, manage their digital footprint, and analyse their personal data exposure across platforms—all while preserving strict privacy and security standards.
Key Features
- Automated Data Removal: Users submit requests that trigger backend logic to process removal across third-party services and vendors
- Serverless Architecture: Invisio Me runs on Lambda, making it scalable, cost-effective, and resilient
- Privacy-First Identity Management: User authentication and session handling are managed via Amazon Cognito and IAM, ensuring secure and controlled access
- Real-Time Frontend: A lightweight, responsive frontend powered by AWS Amplify, integrated with Elastic Load Balancer, API Gateway, and CloudFront for global performance and reliability
- Query Submission Pipeline: Requests are processed and routed through Step Functions for orderly coordination and automation of complex workflows
- Analytics & Intelligence: Query results and removal progress are logged in S3, indexed with ElasticSearch, and made available for deep analysis via Athena
- Monitoring & Governance: Full transparency via CloudWatch and CloudTrail, to support auditing, compliance, and debugging
Tech Stack
- Frontend: Amplify, CloudFront, Route 53, Elastic Load Balancer
- Backend: Lambda, Step Functions, API Gateway
- Identity & Access: Cognito, IAM
- Monitoring: CloudWatch, CloudTrail
- Storage & Search: S3, ElasticSearch, Athena
- Workflow Coordination: Step Functions
Purpose
Now more than ever before, data privacy is increasingly at risk, Invisio Me offers a tool for individuals looking to take control of their digital footprint. Not only automating data removal requests but also providing detailed tracking and analysis to ensure transparency. Built entirely on a zero trust, cloud-native architecture.
I will be putting together a step-by-step guide on how to recreate this tool for personal use for likeminded individuals wanting to take back control of their data.